Secure-by-Design
Our architecture ensures the highest level of security based on the following core principles:
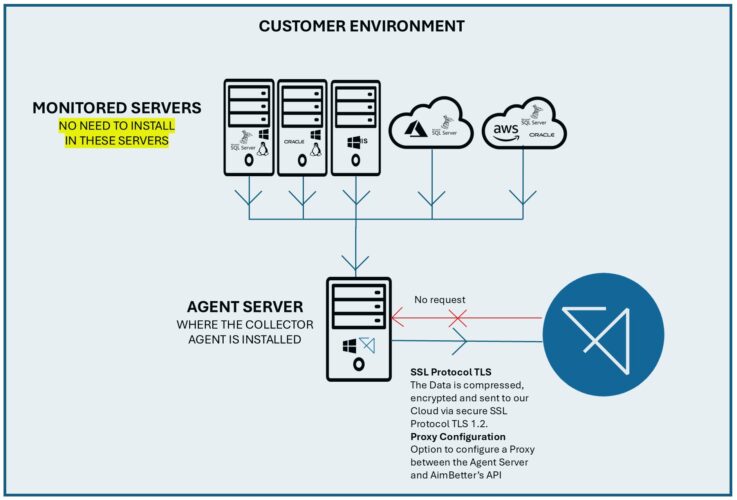
1️⃣ Single Collector Agent with Minimal Permissions
- Installed in the customer’s network
- Runs with minimal resource requirements (non-dedicated Windows host, 2GHz CPU, 1GB memory)
- Light footprint (~0.5% CPU average)
- Least-privilege operation, no direct DB content access (DMV & System Views on MSSQL, $V on Oracle)
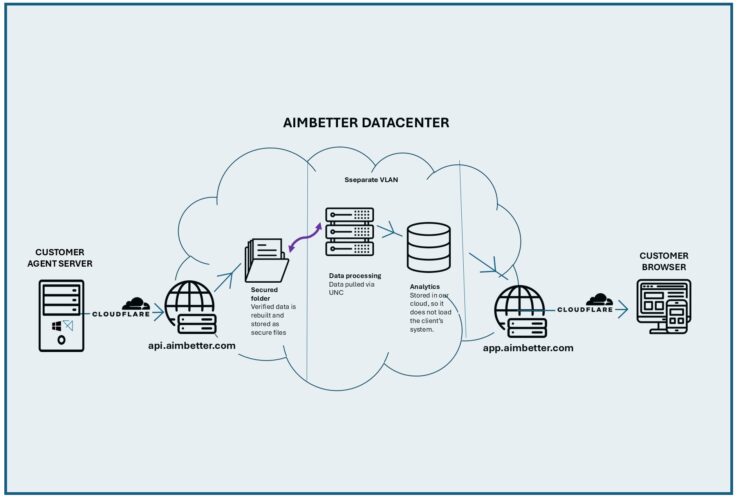
2️⃣ Secure Encrypted Transmission
- All data is encrypted in transit and at rest
- Prevents unauthorized access and interception
3️⃣ Highest Security Standards in a Multi-Tenant* Datacenter
- Complies with leading security frameworks and regulations
- Provides data isolation between tenants using a set of secure protocols
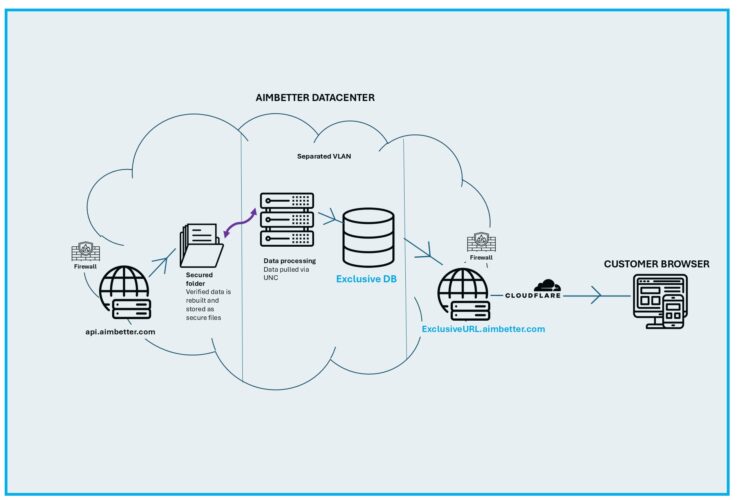
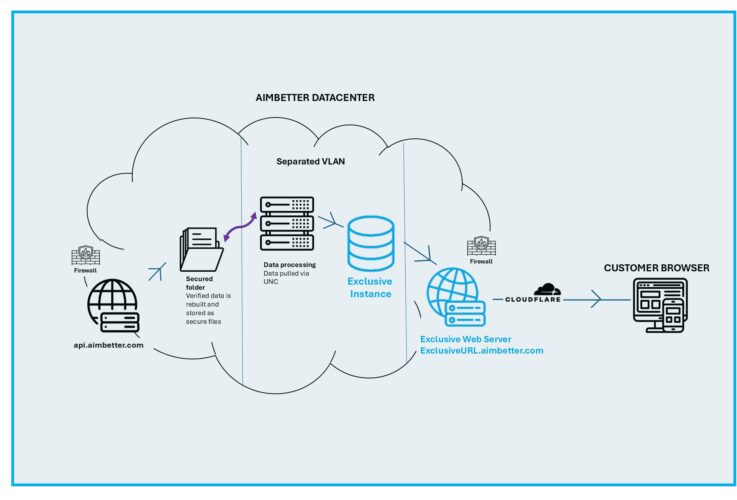
*For customers with more stringent compliance requirements, we offer premium security options
4️⃣ Secure Access to Web Application
- Enforced security controls, including login failure limits, session protection, and IP-based access restrictions
- Support for enhanced authentication methods, including 2FA and SSO
- Windows Servers:
Real-time data on running processes, CPU and memory usage, disk performance, network activity, services, time settings, and system events, based on WMI.
- Linux Systems:
Gathers OS version, active processes, CPU and memory stats, I/O performance, disk and swap usage, network traffic, and service status through standard system commands.
- Microsoft SQL Server:
Collects query execution statistics, wait times, session and transaction activity, index and storage usage, high availability status, and system configuration using DMVs and system views.
- Oracle Databases:
Extracts performance data, including SQL performance, session tracking, job scheduling, storage, configuration, and critical alert logs from V$ views and DBA tables.
You can check all the data sources in the Agent Viewing List
- Every module clearly displays its data collection interval directly in the Agent UI
- Intervals are designed to balance near real-time visibility with minimal system overhead
- Different data types are collected at different frequencies, based on their nature and operational impact
- Modules can be deactivated at any time, giving customers complete control over what is monitored
All data collection intervals are directly exposed in the AimBetter Agent, ensuring that customers can confidently deploy AimBetter in regulated, high-load, and security-sensitive environments, with complete visibility and control at all times.
More about the AimBetter Agent.
These premium security conditions incur additional infrastructure and maintenance costs and require an on-demand quotation based on the customer’s specific needs.